How Elliot & Fsociety Made Their Hack of Evil Corp Untraceable
Well, the first season of Mr. Robot just ended and Elliot and fsociety successfully took down Evil Corp! They have effectively destroyed over 70% of the world's consumer and student debt! Free at last! Free at last!
Although there were many elements that made the hack successful, such as Darlene developing a zero-day exploit (I'll showing you how to do that in a future article) that none of the intrusion detection systems, firewalls, or antivirus softwares detected, Elliot also made certain that the hack could not be traced back to him by using proxies.
Early in the last episode, Lenny, the former boyfriend of Elliot's therapist, Krista, reveals to Krista that he had been hacked by Elliot. He points out that Elliot is nearly untraceable as he uses a proxy from Estonia. In this tutorial, I will show how Elliot bounced his attack off an Estonian (or other) proxy in order to make his hacks untraceable.
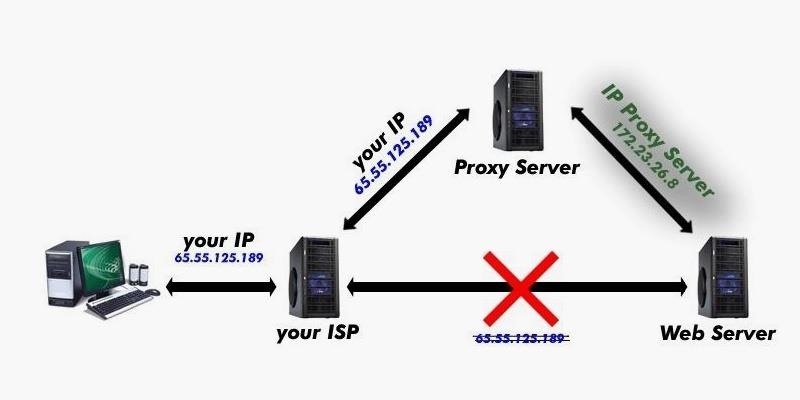
How Proxies Work
As you know, whenever you visit (or hack) a website or server over the Internet, your unique Interpret Protocol (IP) address travels with you. It would then be very easy to trace the source of an attack by simply tracing the source IP address.Hackers, though, often use proxies to hide or obscure their IP address. In this way, they send their traffic to an intermediary proxy, who then sends the traffic on to the destination, replacing the source IP address with its own. In this way, the malicious traffic appears to be coming from the proxy and not the original sender.
Step 1Fire Up Kali
To get started, fire up Kali Linux. If don't already have Kali, you can download it here.Step 2Go to Proxychains
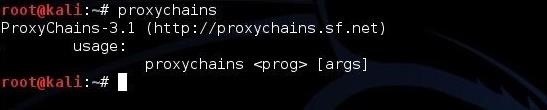
Next, let's go to proxychains. Type:kali > proxychains
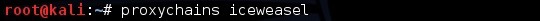
When you do so, it shows you the simple proxychains syntax. Basically, after setting up proxychains, all you need to do is precede the command you want to run with the command "proxychains" and all of your Internet traffic will go through your chosen proxy. As we will see later in this tutorial, if we want to browse the Web with our browser, we can simply start our browser by preceding it with proxychains, such as:
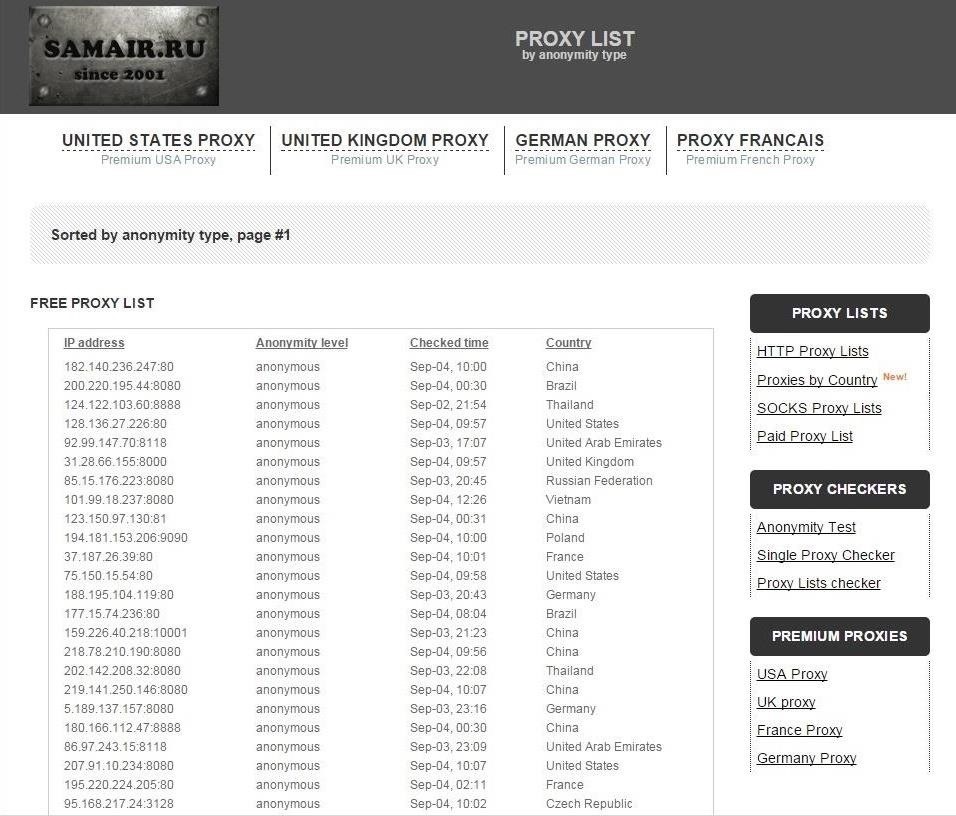
Step 3Search for Proxies
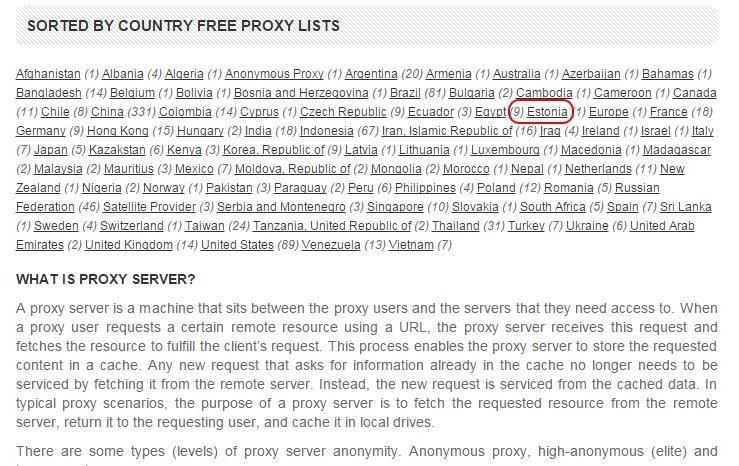
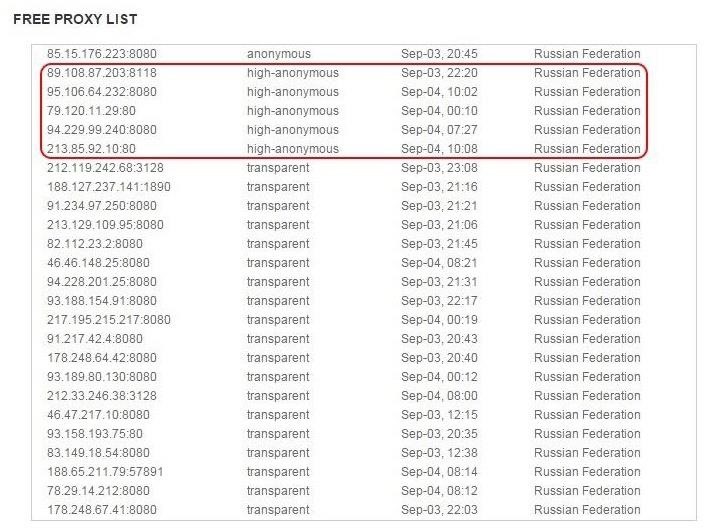
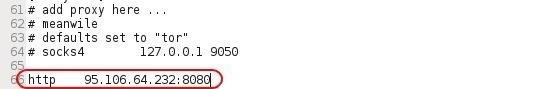
In order to set up proxychains to hide our IP address, we will need to select a proxy. There are many sites on the Web with lists of free and paid proxies. Some of these include, but are not limited to:Let's try using SamAir Security. When we navigate there, we can see their list of free proxies.
Step 4Configure Proxychains
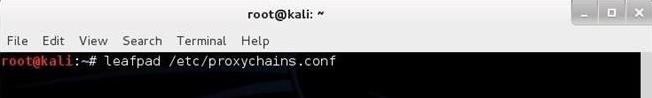
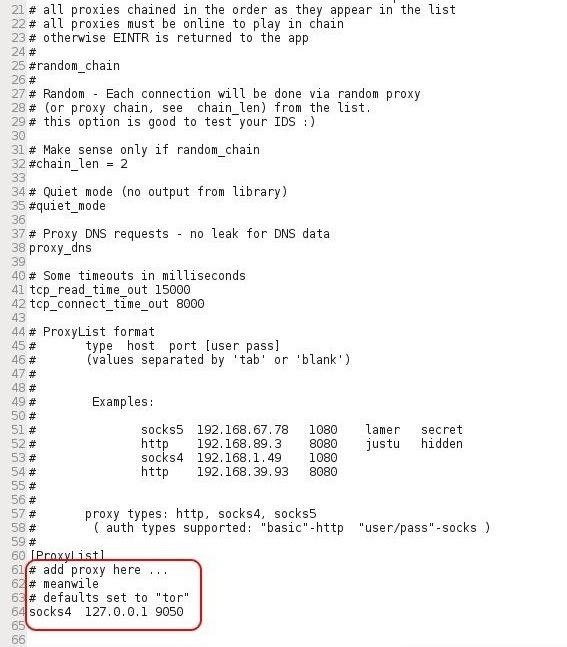
Now that we have a list of potential anonymous proxies, we have to configure proxychains to use it. Like nearly all Linux/Unix applications, configuration is done by a plain text file. These files are generally found in the /etc directory. In this case, the configuration file for proxychains is found at:/etc/proxychains.conf
kali > leafpad /etc/proxychains.conf



Comments
Post a Comment